government agencies
Cryptophones are 100% secure thanks to the certified military grade 256bit encryption at the base of their operating system.
NIAP / FIPS VALIDATED SOLUTIONS
When it comes to national security, law enforcement and strictly personal communications, there must be no margin for error or the possibility of intrusion, both by criminals and by people outside the context in which the information exchange takes place. We want to provide authorities and government agencies with the highest available standards of safety and reliability, as well as independence from any unaffected third parties.
total privacy for your communications
END-to-END certified encryption
The information stored on the device and all data transfers are encrypted with military-grade encryption technology to prevent unauthorized access to third parties.
total operative system protection
Our operating system was developed by analyzing all possible threats. It is constantly updated and enhanced to ensure constant protection from any threat.
military-grade security level
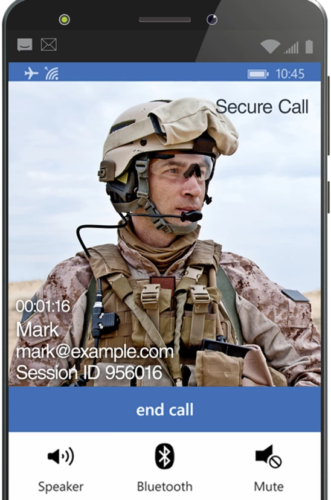
We use military-grade encryption and security systems to protect you from the most hostile threats. Communication takes place in total safety between the two associated devices.
multi-level defense of the device
Separate authentication at the operating system level protects every component of the phone in real-time, such as the hard drive, the operating system, and the various applications that run on it.
SAFE COMMUNICATIONS FOR US AND GOVERNMENTS
DEFENSE DEPARTMENTS AND ARMED FORCES
Both are areas in which you must be able to rely on equipment that allows you to communicate secret and strategically important information in real time, both at home and abroad.
Sometimes military personnel must also exploit public networks, when private ones are not available, thus operating in environments that expose them to wiretapping and attacks.
Widely used by the military for special operations, Cryptedphones can be used in a variety of fields to enable secure and encrypted communications.
NATIONAL SECURITY
Secure communication is necessary to respond to disasters and to manage the post-event. These scenarios often involve the exchange of sensitive information between mobile devices and public access networks, giving the possibility, even in this case, to external intrusions.
PUBLIC ORDER AND LAW FORCES
Today’s law enforcement and counter-terrorism forces must be able to communicate promptly with government departments, including international, national, regional, and local ones.
Communication with first responders and emergency services is key, especially to prevent problems from escalating.


INTELLIGENCE
your privacy above all
The phone is encrypted both as an operating system and as voice and chat applications, with military 256-bit encryption, end to end. This prevents, even the owners of the infrastructure, from decrypting calls and / or messages, since the encryption keys are generated by the end-points and are different for each message or call.
The phone is encrypted with the following: AES-256-GCM for data, AES-256-CBC for metadata
Applications are system apps, i.e. applications inserted directly into the secure ROM. This gives greater security in the event of complex attacks where servers and application update infrastructure are compromised, in which the attacker is able to recompile applications with malicious code. In these cases the update with the malicious code is not successful but is rejected, giving an error such as POP-UP.
Furthermore, these devices use the hardware Titan-M Chip mounted on the SoC to perform security checks when the phone is booted, and create a chain of digital certificate trust, starting from an AES-256 token installed on the TITAN-M chip (the generated token is saved on our off-line infrastructure, also encrypted with AES-256).
The phone cannot be positioned, and no one is able to associate it with a natural person using the SIM provided. Furthermore, even in the event of loss, seizure or theft, it is impossible to access the phone.
The phone cannot be positioned, and no one is able to associate it with a natural person using the SIM provided. Furthermore, even in the event of loss, seizure or theft, it is impossible to access the phone.
